Intel CPU Defect Lawsuit
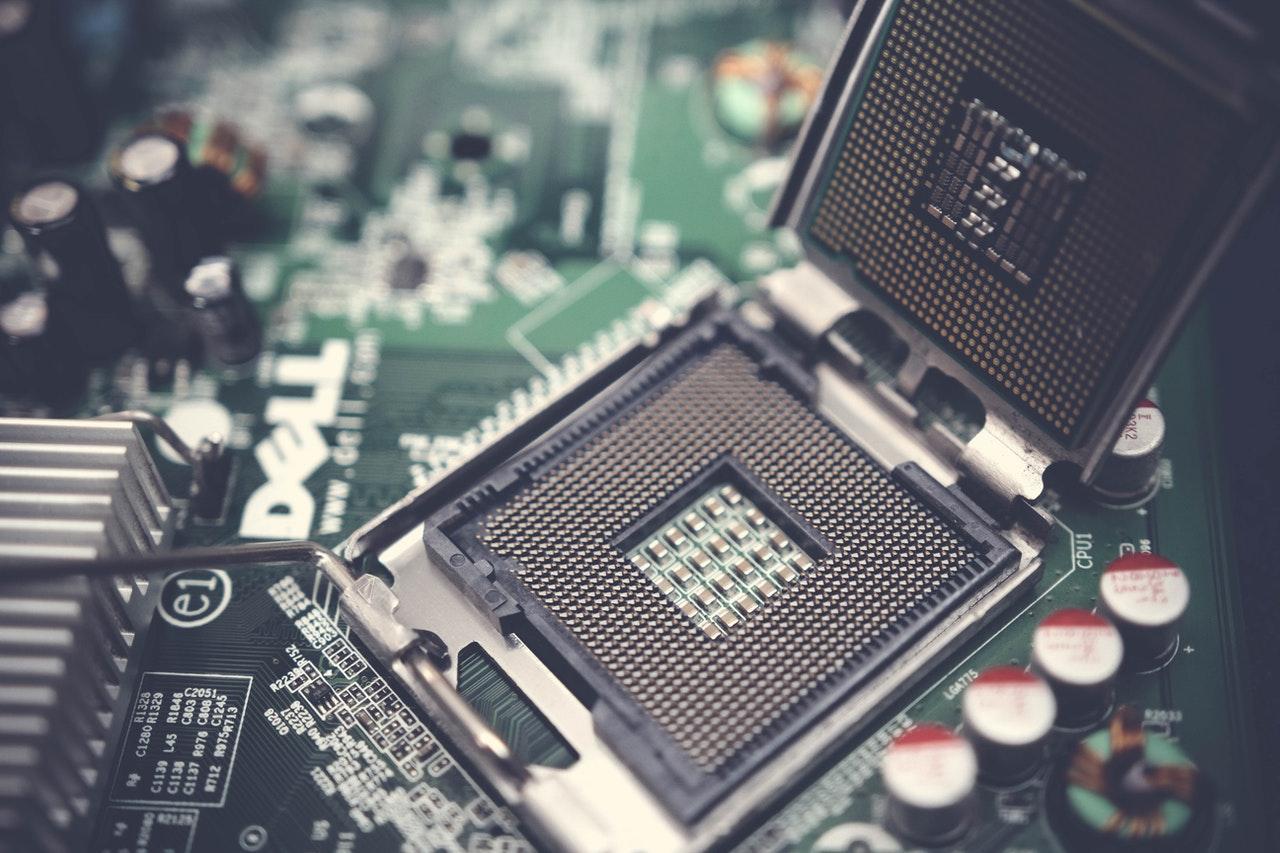
Gibbs Mura, A Law Group, and co-counsel represent consumers in a class action lawsuit against Intel alleging that many of its CPUs have serious security flaws. On January 3, 2018, news reports broke that security researchers discovered two major security exploits in nearly all of Intel’s chips, used in many laptops and desktops. Although software makers attempted to create patches for these flaws, they significantly slow down performance when installed and may not provide complete protection.
If you own a laptop or computer with an Intel CPU, you may have a claim.
Intel CPU in your desktop, laptop or server?
You may have a claim. Speak with our award-winning consumer protection attorneys.
List of Intel Processors at risk
These Intel chips are alleged to have serious security flaws:
- Intel Core i3, all generations
- Intel Core i5, 1st generation through 8th generation
- Intel Core i7, 1st generation through 8th generation
Intel CPUs are used in many brands of laptops and desktops, including Dell, Lenovo, HP, and Apple Macbooks (until 2020).
Despite knowing about these flaws, Intel allegedly continued to sell and distribute these chips.
Intel chips still vulnerable to Spectre and Meltdown flaws
As recently as May 2021, Ars Technica reports that researchers have found attacks that can still break through a vulnerability in Intel CPUs known as Spectre.
Both Spectre and Meltdown are major security vulnerabilities in Intel CPUs first described in 2018 by four independent teams of security researchers. According to the security researchers, all Intel CPUs are exploitable by Spectre and nearly all Intel CPUs made since 1995, except for Itanium chips and pre-2013 Atom chips, are exploitable by Meltdown.
As the complaint alleges, hardware flaws make all software built on top of it vulnerable. Though different operating systems like Microsoft and Linux have released patches to make Intel’s vulnerabilities harder to exploit, these patches often slow down computers “significantly” and they may not solve the security problems completely.
Many computer experts blame Intel for prioritizing speed and performance over security. According to The Guardian, Intel chips “were optimized for performance, without basic questions being asked about whether their design was secure.”
Our Consumer Protection Attorneys
Rosemary Rivas
Rosemary is devoted to obtaining justice for consumers in lawsuits involving claims of false advertising, defective products, and privacy violations.
View full profileEric Gibbs
A founding partner at the firm, Eric has negotiated groundbreaking settlements that favorably shaped laws and resulted in business practice reforms.
View full profileAndre Mura
Andre represents plaintiffs in class actions and mass torts, including in the areas of consumer protection, privacy, and products liability.
View full profileAaron Blumenthal
Aaron represents consumers, employees, and whistleblowers in class actions and other complex litigation.
View full profileAbout Us
Gibbs Mura, A Law Group is a California-based law firm committed to protecting the rights of clients nationwide who have been harmed by corporate misconduct. We represent individuals, whistleblowers, employees, and small businesses across the U.S. against the world’s largest corporations. Our award-winning lawyers have achieved landmark recoveries and over a billion dollars for our clients in high-stakes class action and individual cases involving consumer protection, data breach, digital privacy, and federal and California employment lawsuits. Our attorneys have received numerous honors for their work, including “Top Plaintiff Lawyers in California,” “Top Class Action Attorneys Under 40,” “Consumer Protection MVP,” “Best Lawyers in America,” and “Top Cybersecurity/ Privacy Attorneys Under 40.”